Security vulnerabilities stories - Page 22

Stop patching Spectre & Meltdown issues or risk reboot problems, Intel warns
Thu, 25th Jan 2018
#
intel
#
security vulnerabilities
#
patching
Intel is warning all users to stop downloading patches for the Spectre and Meltdown vulnerabilities because they are causing system reboot issues.
Meltdown and Spectre fallout: patching problems persist
Fri, 12th Jan 2018
#
intel
#
amd
#
spectre
Patching difficulties persist as the tech industry grapples with the fallout from Meltdown and Spectre, highlighting flaws in nearly all modern processors.

Intel CEO addresses Spectre and Meltdown bugs at CES keynote
Wed, 10th Jan 2018
#
semiconductors
#
intel
#
spectre
Kraznich advised users to apply any updates from your operating system vendor and system manufacturer as soon as they become available.

Intel processor vulnerabilities: What you need to know about Meltdown and Spectre
Mon, 8th Jan 2018
#
semiconductors
#
microsoft
#
google
Desktops, laptops, and smartphones running on vulnerable processors can be exposed to unauthorized access and information theft.
GitHub to boost security tracking for developers' projects
Fri, 13th Oct 2017
#
martech
#
apm
#
open source
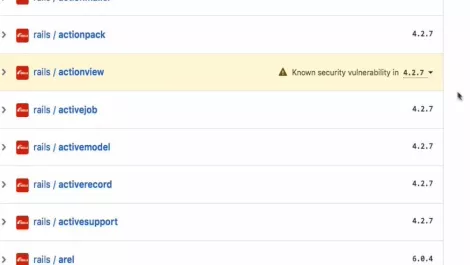
GitHub has unveiled security improvements that will allow developers to track which dependencies are associated with public security vulnerabilities.

Apple's EFI firmware updates leave systems vulnerable
Wed, 4th Oct 2017
#
apple
#
duo
#
security vulnerabilities
Duo Security's study finds troubling gaps in Apple's EFI firmware updates, leaving many Macs exposed to potential sophisticated cyber threats.

Windows 10 security solutions powerless against 'bashware'
Thu, 14th Sep 2017
#
malware
#
open source
#
cybersecurity
Every security solution on the market may be completely powerless to stop a vulnerability that could allow any malware to bypass Windows 10 systems.

Samsung Mobile launches bug bounty program
Wed, 13th Sep 2017
#
cybersecurity
#
samsung
#
security vulnerabilities
Samsung is the latest vendor to jump into the world of bug bounties through the launch of Samsung Mobile Products Rewards Program.

Android 'Toast' overlay vulnerability affects all versions prior to 8.0
Mon, 11th Sep 2017
#
security vulnerabilities
#
cyber attacks
#
technology gifts
Android users are being urged to apply any security patches for their devices, after security researchers discovered a 'high severity' vulnerability.

State-sponsored election hacks are acts of cyber warfare - survey
Mon, 11th Sep 2017
#
elections
#
venafi
#
security vulnerabilities
78% of respondents said they would deem an act as cyber war if a nation-state was behind a successful or attempted hack of another country's election.
$500,000 zero-day prize pool for Mobile Pwn2Own contest in Japan
Fri, 1st Sep 2017
#
trend micro
#
zero day malware
#
security vulnerabilities
Trend Micro has put more than US$500,000 towards a prize pool that aims to find security vulnerabilities at the upcoming Mobile Pwn2Own contest.
DRS CEO: “There are 3 groups of hackers: black, grey and white.”
Wed, 12th Jul 2017
#
hackers
#
security vulnerabilities
#
dynamic recovery services
Most of us get a mental image of an anonymous, hooded figure, bent over a computer in some dark recess of the web when the word hacker is mentioned.

Four cyber security principles that withstand the test of time
Thu, 6th Jul 2017
#
endpoint protection
#
edr
#
software development
Information security can be a noisy place. As a career security guy my experiences have given me a deep understanding of attackers & the enterprise.

Here's why WannaCry might be the tip of the iceberg
Wed, 7th Jun 2017
#
malware
#
ransomware
#
cybersecurity
Much ink is still being expended trying to determine who was responsible for WannaCry and what their motives were. But there's a bigger lesson here.

Strategy for cyber crime: own the routers, own the Internet
Mon, 10th Apr 2017
#
router
#
carbon black
#
opinion
Mobile devices & smart TVs controlled by cyber criminals make scary headlines. There's something scarier – the possibility that routers can be owned.

Ransomware was 2016's hottest ticket as attacks spiked to whopping 752%
Mon, 13th Mar 2017
#
malware
#
ransomware
#
cybersecurity
Ransomware has seen a 752% increase in use over 2016, resulting in $1 billion in losses for enterprises worldwide.

Trustwave exposes backdoor in DblTek devices; vendor issues poor patch & goes silent
Mon, 6th Mar 2017
#
uc
#
voip
#
contact centre
DblTek left vulnerabilities in its IoT devices, tried to hide the vulnerability, issued shoddy patches and cut off all contact with Trustwave.

The stats are in: Japanese PC users at risk of attack through old and unpatched software
Tue, 28th Feb 2017
#
flexera
#
security vulnerabilities
#
patching
The average private user has 63 programs on their PC from 21 different vendors. 7% of those are at the end of their life, meaning they're not patched.

Ransomware exploit kits pose huge risk for unpatched organisations
Thu, 13th Oct 2016
#
malware
#
ransomware
#
cybersecurity
Ransomware exploit kits are making it easier for attackers to target enterprises, because they're so simple to enact, Trend Micro warns.
How a Microsoft Edge hole spread 'malvertising' & stayed off the radar
Thu, 15th Sep 2016
#
microsoft
#
trend micro
#
microsoft edge
Proofpoint and Trend Micro have discovered a large-scale 'malvertising' campaign through Microsoft Edge, enacted by threat actors known as AdGholas.